Introduction
In today’s fast-moving digital workplace, automation is everywhere, from onboarding workflows to leave approvals, expense reporting, and employee data syncs. As a PeopleOps leader, you rely on these custom automations to scale, reduce manual effort and maintain a smooth employee experience.
But there’s a hidden risk: when platforms and tools get updated, your custom automations may suddenly break, fail silently, or misbehave, causing chaos instead of efficiency.
In this article we’ll cover:
- Why custom automation breakage happens when updates roll out
- The pain points and risks it introduces for People & Operations teams
- Proven strategies and best practices for “hardening” automations, so they stay resilient when systems change
- A concrete real-world scenario from a PeopleOps / SaaS environment
- How your PeopleOps team can partner with Engineering/IT to make this work
Why updates break custom automations
Custom automations often plug into third-party systems (HRIS, ATS, Slack, Salesforce, SAP, Workday etc.) or internal tools. When one of those systems issues an update, maybe a UI change, API version change, deprecated field, changed event trigger, or new security setting, your automation logic can fail.
Key failure modes:
- Changed API endpoints or payload schemas: e.g., HRIS sends
employeeIdfield changed toemp_id→ your automation can’t parse it. - UI/selector changes (for UI-based automations / RPA): The button or section your bot clicked is moved/renamed → automation stops.
- Platform version upgrade/back-end changes: New version disables previously supported trigger event.
- Dependency or library update: A library you used in the automation script is upgraded and changes behavior/throws new errors.
- Permissions/roles changed: The account used by the automation loses a permission after update → failure.
- Change in business logic or data model: E.g., org restructuring means new fields are added/old ones removed → automations mis-map.
These breakages cause pain: unexpected outages, manual workarounds, frustrated employees, lost trust, compliance risks, and time lost in troubleshooting.
The PeopleOps pain-points when automations break
From a PeopleOps perspective, broken automations translate into real problems:
- Onboarding flows get stuck: new hires don’t get access, managers don’t get tasks, HR has to manually intervene.
- Offboarding automations miss steps: revoked access gets delayed → security/compliance risk.
- Report generation fails silently: People leaders don’t see updated data or metrics.
- Employee experience suffers: E.g., leave request automation mis-routes or fails → employees are frustrated.
- Scale hindered: What was a “set-and-forget” automation now needs manual oversight.
- Confidence in automation drops: Teams revert to manual work, losing the time-saving benefits.
For PeopleOps teams aiming to be strategic, reliable automation is a foundation — if it fails unpredictably, you lose credibility and operational advantage.
Hardening custom automations: What does it mean?
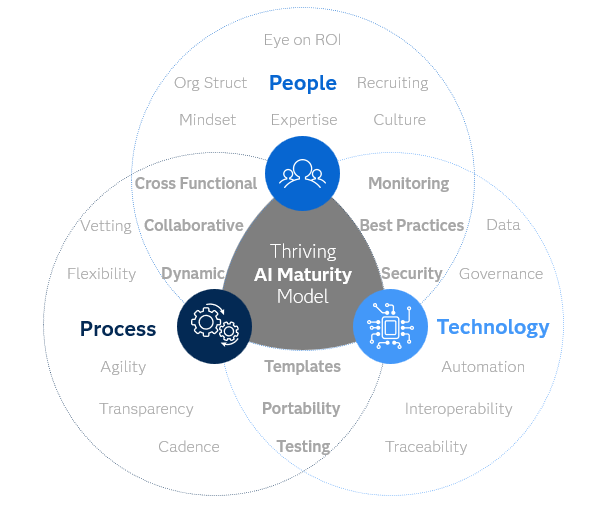
“Hardening” in this context means: designing, building and maintaining your automations such that they are resilient, fail-gracefully, monitored, and adaptable, especially in the face of updates to systems they rely on.
It borrows from the broader concept of system hardening (securing and stabilising IT systems) but applies to automation workflows and integrations. WebAsha+2puppet.com+2
In other words, rather than building automation and ignoring it, you build with update-risk in mind: you assume updates will come, and you build mechanisms to catch, adapt and recover from them.
Best practices for hardening custom automations
Here are concrete strategies that PeopleOps teams, working with IT/Engineering, should adopt.
1. Maintain an inventory of automations, dependencies & systems
- Document every automation: what it does, which systems it touches, what triggers it, what accounts it uses, what data it expects.
- List dependencies: APIs, data fields, UI selectors, libraries, environment variables.
- Track upstream systems and their update cadence: for example, your HRIS vendor’s release schedule, major version changes, deprecations.
This aligns with patch/asset-inventory best practice: “You can’t protect what you don’t know exists.” blog.invgate.com+1
2. Build automation with abstraction and loose coupling
- Wherever possible, avoid hard-coding UI selectors, field names, accounts, or versions. Use variables, configuration files, aliases.
- Use modular components: e.g., a data-fetch module, a transform module, a trigger module. If upstream changes, you only need to update one module.
- Use versioned APIs and avoid “latest” un-versioned endpoints when available.
- Add interface/wrapper layers so that when underlying system changes, you only update your wrapper instead of rewriting whole workflows.
3. Testing environment & regression testing before roll-out
- Set up a “sandbox” or staging version of upstream systems (HRIS, ATS, Slack, etc) for testing automation changes.
- Whenever upstream vendor publishes an update (or you anticipate one), deploy your automation to the test system and run a regression suite: test all automations end-to-end.
- Automate tests wherever you can (unit tests, integration tests, UI script tests) so you detect breakage early. This is aligned with best-practice patching: “Maintain a testing environment… Even if no custom software, evaluate patches before deployment.” TechTarget
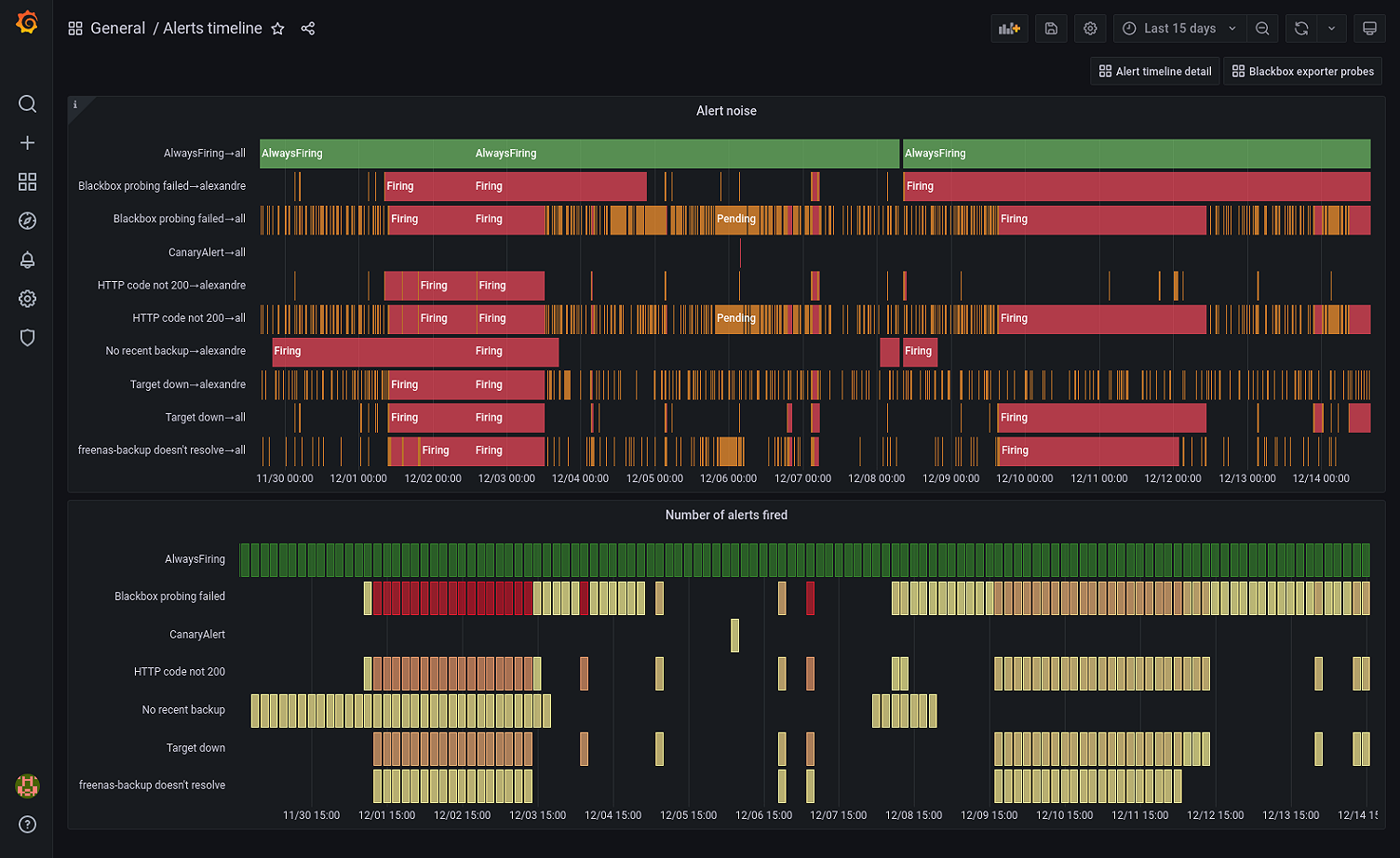
4. Monitoring, alerting & fallback / graceful degradation
- Build monitoring around your automations: track success/failure counts, response times, logs, exceptions.
- On failure, send alerts (email, Slack, dashboard) to PeopleOps + engineering.
- Graceful degradation: if automation fails, have a fallback path (e.g., send notification to a human that manual action is required).
- Maintain a rollback / recovery plan: ability to disable the automation or revert to prior version if an update causes widespread failure.
5. Version control, documentation & change management
- Keep your automation scripts/config in version control (Git, etc) with clear logs of changes.
- Document the logic, the trigger, the data mapping, the expected outputs.
- Use change-management: when an upstream system announces an update, schedule a review of impacted automations, plan testing, schedule deployment.
- Use tags/labels for major version releases of automations, so you can roll back to prior stable version.
6. Prioritisation & scheduling of updates
- Not all upstream updates are equal. Prioritise automations that support critical workflows (onboarding, offboarding, compliance) for early testing when upstream updates roll out.
- Schedule your automation changes outside of business-critical windows.
- Leverage vendor update calendars (if available) and freeze changes ahead of major vendor releases to reduce risk.
7. Collaboration between PeopleOps, IT/Engineering and Vendor / Tool teams
- PeopleOps owns the what (which workflows need automation, what business logic applies) and monitors outcomes.
- Engineering/IT owns the how (scripts, APIs, testing, monitoring, version control).
- Vendor/tool teams should provide release notes, changelogs, sandbox environments.
- Regular cross-team meetings: review upcoming vendor release notes, assess impact, share inventory of dependent automations.
Real-world scenario: PeopleOps at a SaaS company
The setup
Imagine you are a PeopleOps manager at a mid-sized SaaS company. You have a custom automation: when a new hire is added in your HRIS (say Workday), your integration triggers: create Slack account, assign to email group, schedule welcome tasks, assign required training, create Jira tickets for equipment, add employee to organisational chart.
This automation uses:
- HRIS webhook on “employee created”
- Slack API (creating user, adding to channels)
- Jira API (create tasks)
- Internal script written in Python, deployed in AWS Lambda, triggered by the webhook
The update & failure
Your HRIS vendor rolls out a major version bump. They change the webhook payload: they rename field new_employee_id to employee_uuid, and move the email field under contact.email_address. They also deprecate the old version of the API after 30 days.
Your automation script still expects new_employee_id and tries to read email directly, so the transform module fails with a KeyError, the Lambda throws an exception, Slack account isn’t created, onboarding tasks don’t trigger, the manager and new hire get no welcome email. PeopleOps gets pulled in manually to fix everything, productivity hit, bad experience, frustration.
The hardening solution
- Because you documented the automation and set up a sandbox environment, you already knew the vendor update was coming. You scheduled a “dry run” in staging one week earlier.
- You had an abstraction layer: your script read
employee_identifier(aliased variable) instead of field names directly. So you updated that alias mapping, re-tested, everything passed. - Monitoring flagged an error on Thursday night rather than Friday business hours. The alert went to PeopleOps + Engineering Slack channel. Engineering rolled back to previous version (via version control) and the fallback triggered a “manual onboarding required” message to the manager. Business continuity maintained.
- In production, you deployed update during a low-traffic window Saturday early morning, operations unaffected.
The benefits
- Zero onboarding failures during major upstream update.
- PeopleOps retained trust in automation.
- Engineers had controlled time to update scripts rather than firefighting on Monday morning.
- Manual intervention minimal, saving hours of person-time and avoiding employee frustration.
How PeopleOps can drive this hardening practice
- Champion the inventory: Ask team leads for all automation workflows, dependencies, tool-integrations. Maintain a shared spreadsheet or lightweight tool.
- Establish an “Automation Maintenance Calendar”: track upstream vendor release windows, upcoming changes to tools you rely on.
- Define SLA for critical automations: e.g., onboarding/offboarding automation must have < 15 min failure detection and alerting.
- Request monitoring & alerting: work with IT/Engineering to ensure every automation logs success/fail status and triggers alerts.
- Set policy for updates: e.g., “No changes to automation production version without testing in staging.”
- Run quarterly drills: simulate vendor-change scenarios and see how automation responds. Improve accordingly.
- Partner with IT/Engineering: You own the business logic, they own technical design. Be part of every upstream vendor release review meeting.
Summary & key takeaways
- Custom automation is a powerful enabler for PeopleOps but without resilience, it becomes a vulnerability when upstream systems change.
- Hardening involves inventorying dependencies, building abstraction, having testing/sandbox environments, monitoring/alerting, version control/change management, scheduling updates and cross-team collaboration.
- For critical workflows (onboarding, offboarding, compliance), treat automations with the same discipline as production software.
- PeopleOps doesn’t just automate now & forget; you actively maintain and future-proof your workflows.
- The result: reliable automation, less firefighting, better employee experience, and a more strategic PeopleOps team.


Leave a Reply